HTB Pro Labs Ifrit Review
The last HackTheBox Pro Labs scenario I completed was Cybernetics (23 machines), which I used to prepare for PEN-300: Evasion Techniques and Breaching Defenses course and OSEP exam back in 2022. Fast forward to a few weeks ago, I decided to take on another challenge, this time I went to solve Ifrit, one of the smaller Pro Labs in the HTB ecosystem.

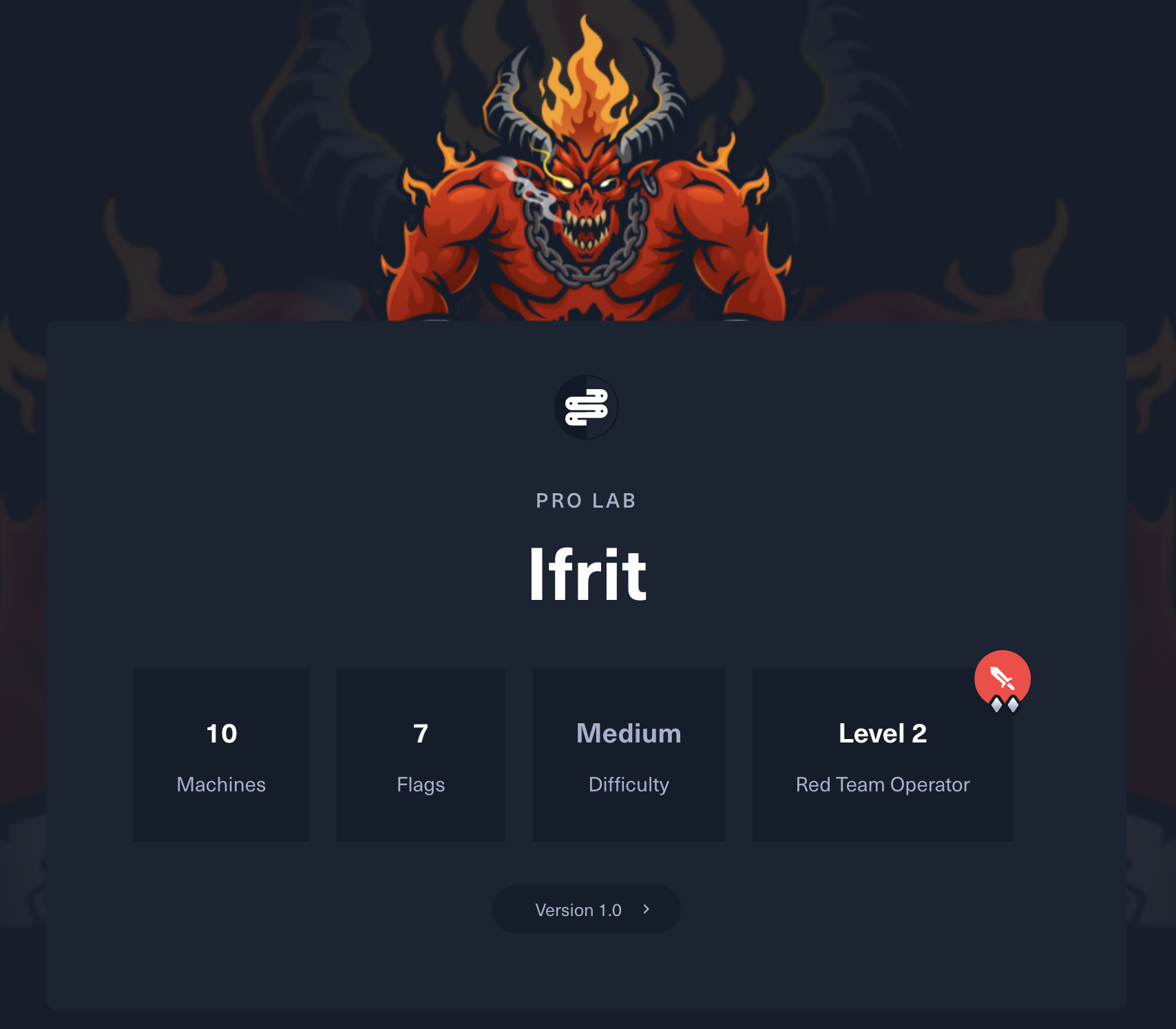
Compared to Cybernetics, Ifrit has a more compact environment, featuring 10 machines and seven flags in total. Despite its size, it offers a highly focused red team experience. According to HackTheBox, Ifrit is classified as a Red Team Operator Level 2 lab with a Medium difficulty rating.
What is Ifrit?
According to the scenario provided by Hack The Box, Ifrit is an IT services company that has recently rolled out a new security baseline across its internal infrastructure. As part of a red team engagement, you’ve been brought in to assess the effectiveness of this baseline. The engagement follows an assumed breach model, meaning initial access has already been granted. To simulate the perspective of a low-privilege insider or compromised endpoint, you’ll start with a VDI (Virtual Desktop Infrastructure) login and a provided list of user credentials. From there, your objective is to navigate through the internal network, escalate privileges, and capture the seven flags located on various Administrator Desktops.

Who Is Ifrit For?
The Ifrit ProLab is well-suited for professionals who already have a foundational understanding of Active Directory and penetration testing and are ready to take the next step into real-world red teaming scenarios.
Prerequisites
- Solid grasp of core penetration testing methodologies
- Basic knowledge of Active Directory architecture and attack techniques
Attitude & Mindset
- Willingness to invest time in research and experimentation
- Patience to troubleshoot dead ends and pivot creatively
- A mindset geared toward thinking outside the box and operating like a real red team operator
What will you gain?
By the end of this lab, you’ll walk away with a solid understanding of how to covertly compromise and maneuver through a modern Active Directory environment. You’ll also sharpen your ability to stay undetected while performing real-world red team operations. Key areas of expertise include:
- Internal Network & Active Directory Enumeration
- Custom Exploitation in an AD Environment
- Attacking Active Directory Certificate Services (AD CS)
- Lateral Movement Across Multiple Forests
- EDR Bypass Techniques
- Relay and NTLM-based Attacks
- Operating Stealthily Within a Domain
Skills You’ll Need (and Build Along the Way)
Throughout the engagement, you’ll strengthen your skills in:
- Using tools like BloodHound, Proxychains, Certipy, MSF, Mimikatz, Rubeus, and Impacket
- Building Kerberos attack chains (S4U2Self abuse, delegation abuse)
- Abusing Active Directory Certificate Services (AD CS) to escalate privileges and gain persistence
- Bypassing modern Endpoint Detection and Response (EDR) solutions using stealthy payloads, in-memory execution, and signature evasion techniques
- Leveraging Windows Event Logs to detect or avoid detection
- Tunneling traffic using proxies and port forwards
- Chaining custom scripts for automation
- Conducting realistic post-exploitation activities
- Crafting operationally secure attacks under assumed breach conditions
What Do You Get After?
Besides the pure satisfaction of completing this awesome lab
- You'll earn an awesome HTB Ifrit Pro Lab certificate of completion
- Gain 40 ISC2 CPE credits to maintain your certifications

My Overall Experience
I really enjoyed solving Ifrit ProLab. With prior experience from labs like Cybernetics, I initially underestimated the smaller number of machines in Ifrit. However, I quickly realized that its compact size was compensated for by its depth and complexity. The lab environment was carefully designed to simulate a modern enterprise network with layered defenses, segmented trusts, and a realistic mix of user misconfigurations and hardening measures. I particularly appreciated how Ifrit emphasized stealth, situational awareness, and methodical post-exploitation and not just popping meterpreter shells. Several paths required chaining misconfigurations and understanding subtle nuances in Active Directory, ADCS abuse, and Kerberos attacks.
One standout aspect of the lab was the need to pivot across multiple forests while navigating through EDR-protected environments. It truly felt like being dropped in the middle of a live engagement with limited initial access, a constrained toolset, and high OPSEC expectations.
By the end of the lab, I walked away with a stronger red teaming mindset and developed more confidence in executing multi-step attack chains while staying covert.
Final Thoughts
The Ifrit ProLab tested both my technical skills and operational discipline. Despite not being the largest or most complex HTB pro lab, it excels at simulating realistic post-exploitation scenarios that red teamers encounter in modern enterprise environments. Each flag offered a meaningful challenge, from stealthy lateral movement to evading EDR and abusing ADCS. If you’re looking to sharpen your offensive tradecraft under assumed breach conditions, Ifrit is absolutely worth your time.
